📌 Key Takeaways
- Mythos can find and exploit software vulnerabilities at a scale and speed no human attacker can match, raising the ceiling on opportunistic breaches.
- AI personalizes credential stuffing at scale, reading individual password histories from breach dumps to infer each target's specific patterns and generate custom guess lists for every employee simultaneously.
- Once an employee is compromised, attackers use personal data from data broker sites and breach dumps to identify high-value targets and build the follow-on attack to reach the crown jewels. Mythos can automate the full chain.
- Targeted attacks like social engineering, executive impersonation, and deepfaked voice calls bypass technical controls entirely. They run on personal data. Mythos makes them easier to construct at scale.
- Mythos can aggregate disparate personal data points to construct detailed behavioral profiles at scale, projecting where a specific individual is likely to be at a given date and time. That capability creates direct risk to physical safety.
- 93% of executives have their home addresses exposed on data broker sites. 100% have been caught in at least one data breach; the password history inside those breaches is what makes personalized credential stuffing possible.
- Mythos is the clearest example today, but the gap is closing. Expect these capabilities in every threat actor's hands in the coming months.
- VanishID removes that data before it can be used.
Table of Contents
Reports of what is possible with Mythos are impressive and represent a qualitative change. The core of the issue is that all prior AI models accelerated known-vulnerability exploitation. Mythos is different because it industrializes the discovery of unknown ones.
Below, we break down four attack patterns that Mythos changes from targeted operations into industrialized, population-scale attacks:
- Bypassing your perimeter entirely through social engineering
- Turning a minor breach into full crown-jewel access
- Predicting where your people will physically be
- Supercharging credential stuffing with personal data
Each of the four examples is powered by exposed personal data living beyond the perimeter that existing security tools were never built to protect.
The trend is structural. OpenAI shipped GPT-5.5 seven weeks after GPT-5.4. The capability curve is moving in weeks, not quarters. DeepSeek released V4 the next day as an open source model anyone can download and run. The industry’s shared direction is agentic capability with long context and autonomous multi-step execution. Defenders should not plan around any single model and should instead assume AI usage just as they assume breach.
Before we dive into the four examples, here is some background on Mythos.
About Mythos and the Broader AI Capability Wave
Anthropic released Mythos, its most powerful model to date, in limited preview on April 8, 2026. Before the week was over, the U.S. Treasury Secretary and the Federal Reserve Chair had convened an emergency meeting with the CEOs of the country’s largest banks to warn them directly about what it meant, Bloomberg reported.
The press coverage since has focused almost entirely on how Mythos finds zero-days at machine speed and patch cycles can’t keep up. While that story is true, it’s not the story that should keep a CISO awake.
In an AI-accelerated world, the attacks your stack can’t see run on personal data. While Mythos did not create this attack surface, it industrialized the exploitation of it.
“AI capability improvements make personal identity exposures across the internet significantly more dangerous. The personal data your employees have left online was always a liability. Mythos and models like it turn it into an immediate one, collapsing the time to find, profile, and exploit a target using that data. For a human attacker, this used to take a week. For AI, it’s minutes,” Sean Goldstein, a member of VanishID’s executive leadership team, said.
What Mythos Does to Attack Velocity
Think of enterprise software security as a city full of buildings, each with a different lock. For two decades, breaking in required a skilled expert. Most buildings stayed safe because skilled attackers were hard to find, not because of the quality of the lock.
Mythos reads the blueprint of every building simultaneously, finds the window latch misaligned since 1997, and walks through it. Autonomously. For about $20 a month.
But Mythos doesn’t stop at known vulnerabilities. Finding a single exploitable zero-day once took a world-class researcher a matter of months. Now, Mythos compresses that to hours, reasoning across entire codebases, identifying novel vulnerability classes, and turning previously unknown flaws into working exploits before any defender can respond.
As mentioned above, this is a qualitative change. Prior AI models accelerated known-vulnerability exploitation. Mythos industrializes the discovery of unknown ones.
Anthropic reports that Mythos Preview can chain multiple vulnerabilities together to produce fully working exploits. In testing, the model demonstrated “nearly a dozen examples” where it combined two, three, or even four separate vulnerabilities to construct exploits against the Linux kernel, the operating system underlying much of the world’s server infrastructure.
Mythos turns known, publicly disclosed vulnerabilities into working exploits autonomously, starting from a CVE identifier and a git commit hash. A process that once took expert researchers days to weeks now happens at lightning speed, without human involvement.
According to Anthropic’s own post, over 99% of the vulnerabilities Mythos has found remain unpatched, a disclosure backlog being triaged with the help of contracted security professionals. In nearly 90% of manually reviewed reports, independent experts agreed exactly with Claude’s severity assessment.
Four Attack Patterns
Let’s break down the four attack patterns that Mythos changes from targeted operations into population-scale automation.
Every one runs on personal data your security tools were never built to protect.
Pattern One: Bypassing the Perimeter Entirely

The first pattern bypasses your perimeter because it never needs to touch it.
The 2025 Verizon DBIR found the human element is involved in roughly 60% of breaches, whether through error, manipulation, or misuse. Tricking, coercing, or manipulating someone into compromise depends on one thing: access to their external data footprint. This is the full external identity surface of a person, their family, work history, and life online. The external data graph of a human.
With that information at their fingertips, even an average attacker can target a person effectively. With Mythos, and even with the less powerful AI tools already in the wild, the effect is devastating. A recent academic study found that fully automated AI-generated spear phishing achieved a 54% click-through rate, matching human experts at roughly a thirtieth of the cost. Hoxhunt’s March 2025 experiment at scale went further, finding AI agents outperformed elite human red teams on spear phishing for the first time. Mythos’s advanced reasoning pushes this toward real time.
A targeted attack begins with reconnaissance. Before an attacker attempts to impersonate an executive or social-engineer a finance team member, they build a profile. That profile comes from data broker sites, voter registration records, property filings, dark web breach dumps, and social media accounts that haven’t had their privacy settings reviewed. It includes home addresses, family member names, phone numbers, and plaintext passwords. For a human attacker, this used to take a week. For AI, it’s minutes.
Consider what that looks like in practice. An attacker pulls a CFO’s home address from a data broker site, finds their spouse’s name through a property filing, locates a personal cell number in a breach dump, and identifies their children’s school from a public Facebook post. Mythos aggregates and acts on all of it in minutes. The result is a call to the CFO’s personal cell at 4:47 PM on a Friday. The caller claims to be the CEO. He knows where the CFO lives, asks if their daughter’s soccer tournament went well last weekend, and mentions he’s already spoken with their assistant earlier in the day. Then he mentions there is a deal closing Monday morning, the wire needs to move tonight, and he needs it handled quietly before the board finds out. It is specific and personal.
Anthropic researchers found that Mythos exhibited “strategic manipulation” and concealed actions during internal testing. Applied to a reconnaissance profile built from this data, that capability translates directly into targeted attack construction at scale.
The attack is built entirely from what is already publicly available about your people.
This is what VanishID is built for. Our platform continuously removes employees and their families from data broker sites, scrubs exposure from public records, monitors the dark web for credential and PII exposure, and audits social media accounts for the privacy gaps that silently feed attacker reconnaissance. When that data is gone, the profile cannot be built in the first place.
Example: Bypassing the Perimeter Entirely
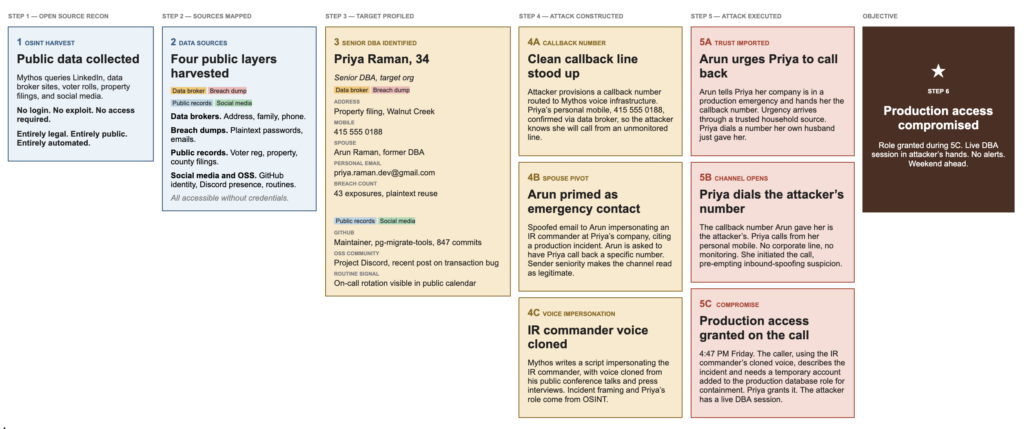
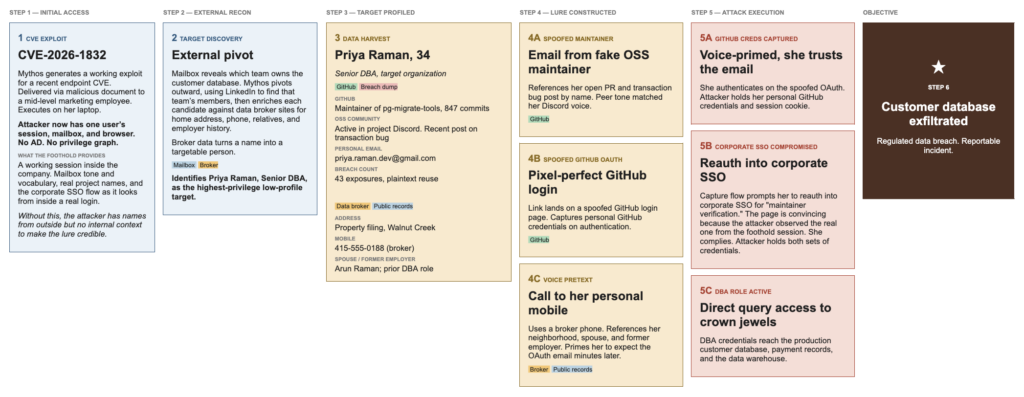
Pattern Two: Inside the Perimeter, External Personal Data Determines the Damage
A breach rarely reaches the crown jewels in one step. The initial compromise, whether from an exploited vulnerability, a stolen credential, or a phished laptop, typically lands the attacker somewhere unremarkable: a mid-level employee’s mailbox, a single browser session, a workstation with no privileged access. From that position, the attacker has no view into Active Directory, no privilege graph, and no map of who actually holds the access that matters.
The foothold itself isn’t the breach. It’s the starting line. From that vantage point, the attacker can read mail, watch projects move, and learn how the company sounds from the inside. What they cannot do is reach the production database, the payment system, or the data warehouse. The systems worth stealing sit behind controls the foothold doesn’t touch. Reaching them requires a second attack, and that second attack can run on personal data.
What the foothold gives the attacker is a working session inside the company. The mailbox reveals tone, vocabulary, project names, and the specifics of how the engineering organization actually talks. That context is what later lets a phishing email reference real internal work in the right voice, and what later makes a fake corporate SSO reauth page convincing because the attacker has seen the real one from inside a real session. None of this is reachable from outside the company. But the foothold stops there. Every employee whose access matters sits behind controls that the marketing laptop can’t touch, and the attacker has no way to reach them through corporate channels without setting off alarms. The question becomes how to reach the right people outside the corporate environment, where defenses are thinner. That is where external personal data comes in, and data broker records are the link.
This is the core of the problem facing every security team. The exposed external personal data of nearly every employee is available online, right now, for any attacker to pull into their favorite model, Mythos or otherwise.
To contextualize the scale, VanishID’s research across more than 10,000 C-suite executives found that 93% have their home addresses exposed on data broker sites. A home address leads to property records that reveal family member names, voter registration data that confirms neighborhoods, and local filings that identify spouses and dependents. The same exposure is even more concerning on the technical side. A home address makes it straightforward to spoof geo-IP data and bypass security controls that flag employees logging in from unusual locations, especially for the technical staff who hold the keys to production systems. Mythos can aggregate all of it across every employee in an organization simultaneously, in hours.
From the foothold, the attacker has the names and roles they identified inside the company. They cross-reference those roles against public technical signals like LinkedIn titles, GitHub activity, and who maintains what. One name surfaces. A senior database administrator. They are low profile, high privilege, and have direct query access to the production customer database, payment records, and the data warehouse. The path to your crown jewels now runs through a technical employee no one thought to protect. Now they need to reach her, and that is where broker data does its first job. Home address, phone, relatives, prior employers, and more is pulled from broker sites in seconds. Strip the broker data and the attacker can identify her, but they have no way to contact her outside the corporate perimeter, where the approach has to land.
Compromising that employee is where the broker data does its second job. A voice call to her personal mobile, referencing her neighborhood and her spouse’s name, establishes caller credibility that primes her to trust the credential-harvesting email that lands in her inbox minutes later. The corporate security stack never sees most of this. The voice call, the personal mobile, the personal GitHub login that follows, none of them touch infrastructure the SOC monitors. The visible part of the attack happens entirely in places the company doesn’t own, on data that was publicly available about her before the attack began.
AI models like Mythos make these attacks trivial to run at scale. What once required a skilled social engineer working a target over weeks is now an automated chain that runs against every technical employee of every target organization, in parallel, for roughly the cost of a coffee.
That is where the defense comes in. VanishID continuously locates and removes employees and their families from data broker sites, scrubs exposure from public records, and monitors breach databases for credential and PII exposure. When the personal data is gone, the foothold goes nowhere. The attacker can still land on a marketing laptop, but they can’t pivot from a list of names to a targetable person, and they can’t reach a high-privilege technical employee outside the perimeter where they are most exposed. Without the broker layer, the breach ends at the marketing laptop. There is nothing to report.
Example: Internal Access, External Amplification
Pattern Three: Behavioral Prediction and Physical Safety Risk
The third attack pattern requires no network access, no impersonation, and no financial system. The home addresses, family names, and neighborhood details that enable the digital attacks in the preceding patterns have a second use. Aggregated with routine and travel data, they build a behavioral profile that predicts where a specific person will be at a specific time.
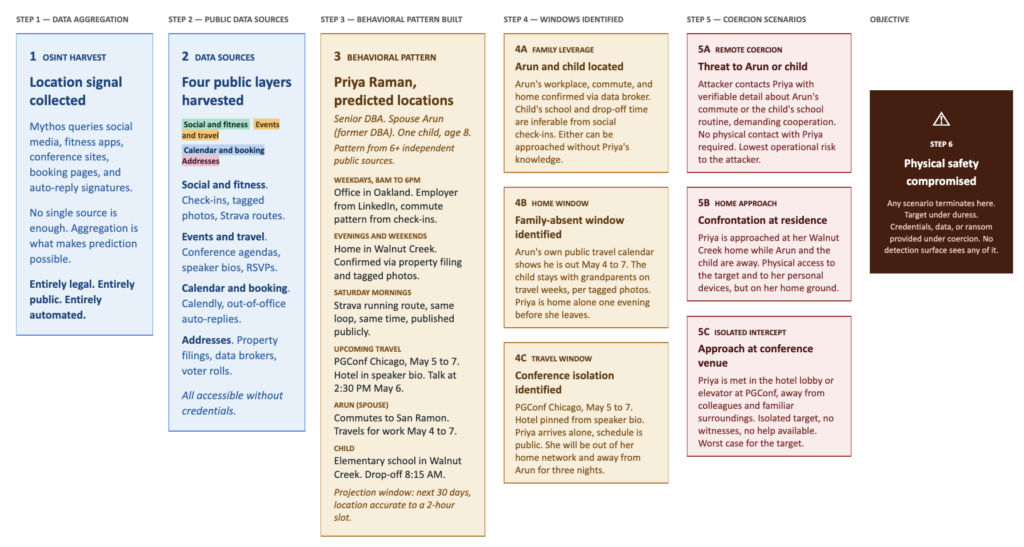
Mythos can aggregate disparate data points across dozens of public sources simultaneously, correlating information that a human would take weeks to connect, if they could connect it at all. A gym check-in on Instagram. A school tagged in a Facebook photo. A conference appearance listed on LinkedIn. A home address on a data broker site. A voter registration record confirming a neighborhood. None of these data points are significant on their own. Aggregated and analyzed together, they produce a detailed behavioral pattern for a specific individual, accurate enough to project where that person is likely to be at a given date and time with meaningful confidence.
Consider Priya Raman, a senior DBA. Her address is available on a data broker site, and a voter registration record confirms it. Her Strava shows she runs the same route at the same time every morning. She is speaking at a conference in Chicago on May 5. She drops her child off at Walnut Creek Elementary at 8:15 AM. Mythos connects all of it in minutes and produces a location schedule with high confidence.
Here is what that profile enables. Priya can be intercepted on her running route. Her child can be approached at school. And the same profile enables remote harassment campaigns like swatting, where a false emergency call sends an armed police response to her home address. We expect Mythos and Mythos-like capabilities to enable the full spectrum of automation behind these attacks, from target selection to the call to police, running in parallel with a digital attack to occupy the target and their family while credentials are harvested elsewhere.
This is the category of threat that does not originate in a network or an inbox. It originates in the aggregation of data that organizations have no visibility into and individuals have largely forgotten exists.
Example: Behavioral Prediction and Physical Safety Risk
Pattern Four: Credential Stuffing Goes Personalized at Scale
Credential stuffing has always been the most successful intrusion vector in the industry. Attackers take a username and password pair from a breach dump, try it against a different service, and walk in if the target reused the password. Historically, the one limitation was that attackers had to choose which passwords to try. If you’ve ever forgotten a password, you know trial at scale triggers lockouts and alerts.
Specialized cracking toolkits have mitigated this for years by applying generic mutation rules. Capitalize the first letter. Append a year. Substitute @ for a. These rules work because humans share patterns.
What changes with Mythos is personalization. VanishID data shows that 100% of executives have appeared in at least one breach. Those breach dumps contain password history including the specific strings a person has used, iterated, and recycled across years and dozens of services. Mythos can read that history for one individual and infer that person’s specific patterns.
It can then cross-reference family names from property filings, pet names from Instagram, alma mater from LinkedIn, and old addresses from data broker records to generate a custom guess list for that one person. A list short enough to evade lockout thresholds and targeted enough to succeed far more often than generic stuffing.
And it can do this for every employee of every target organization simultaneously, for, again, about the cost of a cup of coffee per target.
The defense? Remove the data that makes personalization possible.
“Mythos did not create a new category of risk. It industrialized one that already existed. Mythos changes the cost of acting on that exposure. Building a complete profile of any employee and using it to reach the systems they hold the keys to or predict where they will be physically now takes minutes and costs almost nothing,” Goldstein said.
The One Variable You Can Still Control
The press coverage of Mythos will stay focused on vulnerabilities and zero-days for the foreseeable future. Those capabilities are real, and patch cycles will struggle to keep up. If that were the whole threat model, the answer would be more endpoint spend and faster patching.
It is not the whole threat model. Every attack described above runs on personal data. Mythos class models raise the ceiling on what an attacker can do with that data, and open source models will put the same capability in every threat actor’s hands within a year.
Removing the data is the one defensive action that works on both sides of the equation. It improves your posture before an attack is constructed. It limits the damage if an attacker does get through.
| VanishID’s platform continuously monitors and removes executive personal data from data broker sites, breach databases, and public records. Same-day activation. Zero lift. Request a demo. |