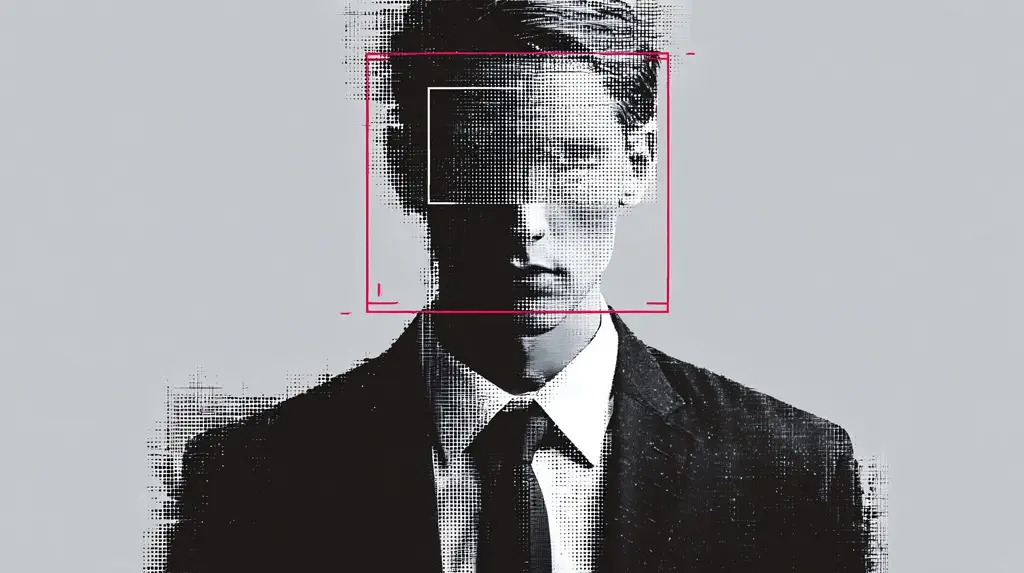
Imagine seeing a video of your CEO authorizing a wire transfer, or worse, appearing in a compromising situation, only to discover it is entirely fake.
The voice sounds right. The facial expressions look authentic. The urgency feels real. By the time anyone questions it, the damage is already underway.
Deepfake technology has moved far beyond internet novelty. It is now firmly embedded in the enterprise threat landscape, evolving into a boardroom-level risk that directly targets leadership. Deepfake extortion scams can manipulate markets, destroy reputations, and cost organizations millions in financial and legal fallout.
From VanishID’s perspective, this shift changes how organizations must think about security. Protecting executive identity and reducing exposed digital footprint are no longer optional. They are now a core aspect of corporate defense.
Understanding Deepfake Extortion and Its Business Impact
Deepfake extortion has become a practical threat, not a theoretical one. As threat actors grow more sophisticated, business leaders need a clear understanding of how these attacks operate and why they so often succeed.
Without that awareness, even experienced executives can be caught off guard by manipulation that looks and sounds legitimate.
What Deepfake Extortion Actually Looks Like
Unlike traditional phishing, deepfake extortion depends on realistic impersonation through synthetic voice or video. The objective is to appear legitimate long enough to trigger action.
Attackers may fabricate damaging footage of an executive, issue ransom threats supported by fake media, or imitate a senior leader requesting urgent payments. These tactics are carefully designed to exploit fear of reputational harm, financial loss, or regulatory fallout.
The effectiveness of deepfakes comes from their realism. When authority appears genuine, normal verification steps are often skipped.
The Shift from Consumer Scam to Corporate Weapon
Advances in AI have made deepfake creation faster, cheaper, and disturbingly realistic. A few minutes of public video or audio is often enough to create a convincing impersonation.
Executives regularly appear in earnings calls, keynote speeches, interviews, and webinars. All of this content becomes training data for threat actors.
High-profile cases already demonstrate the scale of risk, including a widely reported $25 million voice fraud incident in Hong Kong, when deepfakes were used to influence M&A negotiations and to create fabricated announcements that have triggered market confusion.
Business deepfake cyberattacks are no longer hypothetical. They are actively targeting enterprises worldwide, so effective protection against them is essential.

The Unique Dangers of Deepfakes for Executives and Business Leaders
Deepfakes pose a different kind of risk for executives than for the rest of the organization. Their visibility, authority, and public presence make them natural targets for impersonation that can quickly escalate into a broader business issue.
Targeting the Human Layer of Corporate Security
Deepfake extortion scams are effective because they blend into everyday workflows. They do not look like attacks at all. Instead, they resemble routine requests from authority figures.
By introducing urgency or secrecy, threat actors reduce the likelihood that teams will pause to verify what they are seeing or hearing.
Business Deepfake Attacks in Action
Financial fraud is one of the most common outcomes, achieved through fake CEO voices authorizing urgent payments.
Reputational sabotage is another growing tactic, where fabricated videos are leaked to influence public opinion or investor sentiment. In more insidious cases, deepfake leaks are designed to spark internal chaos, trigger executive resignations, or erode confidence during sensitive negotiations.
These scenarios highlight why understanding how to stop deepfakes requires more than technical controls.
Why Traditional Cybersecurity Doesn’t Catch Deepfakes
Most cybersecurity programs are built to stop unauthorized access, not synthetic media. Deepfakes do not trigger alerts because they do not behave like malware.
Instead, they move through approved communication channels, making detection difficult without additional digital executive protection.
The Real Cost of Deepfake Extortion Scams
The impact of business deepfake cyberattacks extends far beyond the initial incident. What begins as a single manipulated video or voice clip can trigger cascading financial losses, reputational harm, and long-term erosion of trust.
For companies, the true cost often unfolds over months, not days.
Direct Financial Impact
The immediate costs of deepfake extortion include wire fraud losses, ransom payments, forensic investigations, and emergency incident response.
These events often demand rapid involvement from legal counsel and crisis communications teams, driving expenses even higher.
Reputational Fallout and Market Consequences
A viral deepfake can erase years of brand equity in hours. Investor trust, employee confidence, and customer loyalty can collapse quickly once authenticity is questioned.
Regulatory bodies may require disclosure, triggering audits or penalties depending on jurisdiction and industry.
The Psychological Toll on Leadership
Beyond financial damage, deepfake scams take a personal toll. Fabricated imagery or audio targeting executives can cause severe distress and distraction.
Leaders may become hesitant to communicate publicly, which can weaken their visibility and confidence at crucial moments.
How to Protect Yourself from a Deepfake? Business Approach
Preventing deepfake attacks requires a shift from reactive defense to proactive risk reduction. Organizations must address both the technical and human aspects of impersonation, especially when it comes to executive identity.
1. Shrink the Executive Digital Footprint
Executives leave digital traces everywhere, from conference videos to podcast interviews. Over time, those traces add up to a usable impersonation profile.
Data removal services reduce how much of that information remains accessible across public databases. VanishID’s platform takes a continuous approach, helping organizations manage exposure as it changes.
2. Establish Identity Verification Protocols
Deepfake attacks often succeed because requests feel familiar. Strong verification protocols disrupt that familiarity.
By requiring confirmation through independent channels, organizations remove the pressure to act solely on appearance or tone.
3. Use Deepfake Detection and Authentication Tools
Detection technology focuses on patterns people miss, such as timing anomalies or unnatural movements. These signals help security teams make faster, better-informed decisions.
When integrated into existing systems, detection strengthens protection against emerging impersonation threats.
4. Prepare Incident Response Playbooks
Waiting to define roles during an incident can create confusion. Deepfake response planning ensures that everyone knows their responsibilities in advance.
Preparation often determines whether an incident is contained quickly or spirals into a broader crisis.
5. Train Employees and Executives
Training is most effective when it reflects real scenarios. Teams should practice responding to unusual requests that feel urgent or emotionally charged.
Understanding how to protect yourself from deepfake manipulation gives employees permission to pause and verify.
How to Stop Deepfakes – Steps to Take Immediately After the Attack
What happens in the first few hours after a suspected deepfake scam appears, often sets the tone for everything that follows. The sooner misinformation is addressed, the easier it becomes to prevent the situation from spiraling.
Verify and Contain
When something does not look or sound right, the most important thing is to pause. Jumping to respond, especially in public, can unintentionally give false content a wider audience before anyone has had time to confirm what is real.
- Have security teams take a close look at the audio or video to determine whether it has been altered
- Set aside original files, messages, and related communications so nothing is lost or overwritten
- Keep distribution tight while the review is underway
- Make sure internal teams are aligned before any public response is considered
Communicate Transparently
Once there is confidence in what happened, it is time to speak carefully. The goal is not to settle every question at once, but to give people enough clarity that rumors do not take on a life of their own.
- Share updates through familiar corporate channels that people already recognize
- Be clear about what is known and what still needs confirmation
- Let employees hear updates directly rather than through side conversations
- Pay attention to how the situation is being discussed externally and correct clear inaccuracies when needed
Engage Law Enforcement and Legal Counsel
Deepfake extortion quickly moves beyond a technical issue. Bringing legal expertise into the conversation early helps organizations stay grounded while decisions are being made.
- Contact law enforcement when the situation warrants it
- Involve legal counsel to guide disclosure and response decisions
- Keep a clear record of actions taken and timelines
- Flag any regulatory obligations that may come into play
Restore Trust and Reassure Stakeholders
After containment, rebuilding confidence becomes the priority.
- Address concerns from investors and partners directly
- Maintain open communication with employees
- Explain changes being made to reduce future risk
- Demonstrate steady leadership throughout recovery

The Strategic Advantage of Proactive Deepfake Defense
Teams that think about deepfakes before they become a problem tend to handle incidents with far less disruption. Preparation is not only about reducing losses, but also about keeping leadership steady when decisions are being questioned in real time.
At the board level, this topic is showing up more often in conversations about responsibility and monitoring. Security leaders who can show that the risk has been considered and planned for usually face fewer surprises when scrutiny increases.
VanishID supports this effort through executive identity monitoring, ongoing exposure reduction, and continuous detection of emerging impersonation risks across public and private data sources.
Conclusion: The Face of Leadership Is the Next Cyber Target
Deepfakes are challenging a belief many organizations have relied on for years: that a familiar face or voice can be trusted by default. The same visibility that helps leaders build authority now gives threat actors material to misuse.
Organizations that reduce unnecessary exposure and make verification routine are better equipped to keep control. In practice, that preparation often determines whether an incident fades quickly or turns into something harder to contain.
To learn how VanishID’s digital protection plans help enterprises reduce executive risk and respond faster to identity-based threats, explore our services or speak with our team today.


